A former senior CIA official has been arrested for allegedly stealing over $40 million in gold bars, raising concerns about internal controls and background checks within the agency.
WASHINGTON — A former senior CIA official has been arrested and charged with stealing more than $40 million in gold bars from the spy agency and concealing them in his Virginia home, federal prosecut… [+6708 chars]
Picture this: You spend weeks quietly perfecting a work project, and then share it with a teammate in absolute confidence. The next day, you find the same colleague in a meeting, taking all the credit. This exact scenario played out in a viral story that has …
Imagine spending weeks working on an innovative project, then your colleague takes all the credit.
Such a situation occurred in a viral story that has people on the internet arguing about corporate … [+6182 chars]
A new CrowdStrike report shared exclusively with Fortune reveals DPRK-linked hackers tripled their attack pace in a single quarter and U.S. financial firms are in their crosshairs.
North Koreas army of cyber operatives stole a record $2 billion in digital assets last year, fueled by the largest financial theft ever reported$1.46 billion stolen in a single operation from crypto … [+8941 chars]
Rolling out to Android devices in the coming weeks, a new security feature will automatically end a phone call from a spoofed bank number.
Lance Whitney/ZDNET
Follow ZDNET: Add us as a preferred source on Google.
ZDNET's key takeaways
<ul><li>This Android feature aims to protect you from banking scams.</li><li>It will detect and hang… [+4594 chars]
Cyberattacks on widely used third-party services like Canvas can expose sensitive data that hackers can later weaponize. Higher education institutions are often a prime target.
A major cybercrime gangs hack of Canvas is highlighting how education technology providers have become attractive targets for cybercriminals, whose access to student records, login credentials and ot… [+4538 chars]
Android malware uses blank icons and fake screens to steal financial credentialstechradar.com
<ul><li>Four Android banking trojan campaigns target hundreds of finance and social apps</li><li>Malware hides icons, blocks removal, and overlays fake banking login screens</li><li>Live screen strea… [+3472 chars]
The crypto theft highlights vulnerabilities in digital finance, potentially prompting stricter regulations and impacting AI's role in cybersecurity.
The post North Korean hackers behind record $635M crypto theft in April 2026 appeared first on Crypto Briefing.
## Market Snapshot
The market concerning “Anthropic Mythos Provision to US Government” reflects a 100% YES pricing across all sub-markets, consistent with recent trends. Meanwhile, the “Ethereum Pri… [+2489 chars]
Security researchers warn of Mirax, an emerging Android banking trojan using MaaS, remote access and residential proxies to target European users
A newly identified Android banking trojan, known as Mirax, is spreading across Europe and combines remote access features with residential proxy capabilities to broaden its impact.
According to an a… [+2791 chars]
Drift has revealed that the April 1, 2026, attack that led to the theft of $285 million was the culmination of a months-long targeted and meticulously planned social engineering operation undertaken by the Democratic People's Republic of Korea (DPRK) that beg…
Drift has revealed that the April 1, 2026, attack that led to the theft of $285 million was the culmination of a months-long targeted and meticulously planned social engineering operation undertaken … [+11316 chars]
If you're the owner of an older iPhone running iOS 18 and are concerned about a dangerous new hacking tool, Apple has a surprising solution.
What makes the DarkSword hacker tool so dangerous is that it tackles multiple iOS vulnerabilities to compromise your iPhone. Typically, attackers go for a Safari/WebKit bug, which then allows these h… [+1311 chars]
Apple is releasing a rare security backport for iOS 18 to protect users from the DarkSword hacking tool. Learn how this exploit works and how to stay safe.
The post Download iOS 18 Patch to Block DarkSword Hack first appeared on iPhone in Canada.
Apple has released a security backport for iOS 18 to protect millions of users from a new hacking tool known as “DarkSword.” As noted by Wired, this emergency patch acknowledges that a significant po… [+2068 chars]
New cybersecurity investigations share a concerning pattern – the weaponization of legitimacy.
The post Report exposes industrial‑scale scams targeting everyday users appeared first on Digital Journal.
Can you trust your ears? AI voice scams rattle US. - © AFP
A new report uncovers three global scam operations that are reshaping the cybersecurity threat landscape. The findings reveal a troubling … [+3579 chars]
A powerful iPhone hacking toolkit dubbed “DarkSword” has been used since November 2025 to compromise devices by exploiting zero-day iOS vulnerabilities, Google researchers have shared. iOS vulnerabilities exploited by DarkSword Two weeks ago, Google Threat In…
A powerful iPhone hacking toolkit dubbed “DarkSword” has been used since November 2025 to compromise devices by exploiting zero-day iOS vulnerabilities, Google researchers have shared.
iOS vulnerabi… [+5481 chars]
Darksword is the second iOS exploit chain in a month
A new exploit kit targeting iPhone users and stealing their sensitive data is being abused by "multiple" spyware vendors and suspected nation-state goons, security researchers said on Wednesday.…<!--#includ…
A new exploit kit targeting iPhone users and stealing their sensitive data is being abused by "multiple" spyware vendors and suspected nation-state goons, security researchers said on Wednesday.
The… [+5407 chars]
A suspected group of Russian government hackers was caught targeting Ukrainians with new iPhone hacking tools designed for espionage and potentially to steal crypto.
A group of hackers suspected of working at least in part for the Russian government targeted iPhone users in Ukraine with a new set of hacking tools designed to steal their personal data, as well as … [+4457 chars]
Over 250 legitimate websites, including news outlets and a US Senate candidate’s official webpage, been compromised to infect visitors with infostealers, warn Rapid7 researchers
A widespread cyber-criminal campaign has compromised legitimate WordPress websites to infect visitors with infostealer malware, threat researchers at Rapid 7 have warned.
The global operation has co… [+3387 chars]
Another week in cybersecurity. Another week of "you've got to be kidding me."
Attackers were busy. Defenders were busy. And somewhere in the middle, a whole lot of people had a very bad Monday morning. That's kind of just how it goes now.
The good news? There…
Another week in cybersecurity. Another week of "you've got to be kidding me."
Attackers were busy. Defenders were busy. And somewhere in the middle, a whole lot of people had a very bad Monday morni… [+33277 chars]
Cloudflare’s network blocks over 230 billion threats per day. The volume indicates how routine and automated the attack cycle has become, and the patterns behind that volume point to a shift in how breaches begin and progress. Cloudflare’s threat research uni…
Cloudflare’s network blocks over 230 billion threats per day. The volume indicates how routine and automated the attack cycle has become, and the patterns behind that volume point to a shift in how b… [+5123 chars]
A new report out from Cloudflare Inc. today warns that cybercrime has reached full industrial scale, with attackers weaponizing the openness of the internet and the connective tissue of cloud and software-as-a-service platforms to move faster and more efficie…
A new report out from Cloudflare Inc. today warns that cybercrime has reached full industrial scale, with attackers weaponizing the openness of the internet and the connective tissue of cloud and sof… [+5268 chars]
A vulnerability in GitHub Codespaces could have been exploited by bad actors to seize control of repositories by injecting malicious Copilot instructions in a GitHub issue.
The artificial intelligence (AI)-driven vulnerability has been codenamed RoguePilot by…
A vulnerability in GitHub Codespaces could have been exploited by bad actors to seize control of repositories by injecting malicious Copilot instructions in a GitHub issue.
The artificial intelligen… [+6912 chars]
A Russia-aligned threat actor has been observed targeting a European financial institution as part of a social engineering attack to likely facilitate intelligence gathering or financial theft, signaling a possible expansion of the threat actor's targeting be…
A Russia-aligned threat actor has been observed targeting a European financial institution as part of a social engineering attack to likely facilitate intelligence gathering or financial theft, signa… [+3905 chars]
Meet ZeroDayRAT, a newly advertised malware targeting Android and iOS devices with surveillance, location tracking, and crypto theft tools sold via Telegram as a MaaS service.
A new mobile spyware platform known as ZeroDayRAT is being marketed through Telegram channels as a subscription-based service that allows buyers to monitor and exploit Android and iOS devices, accord… [+3613 chars]
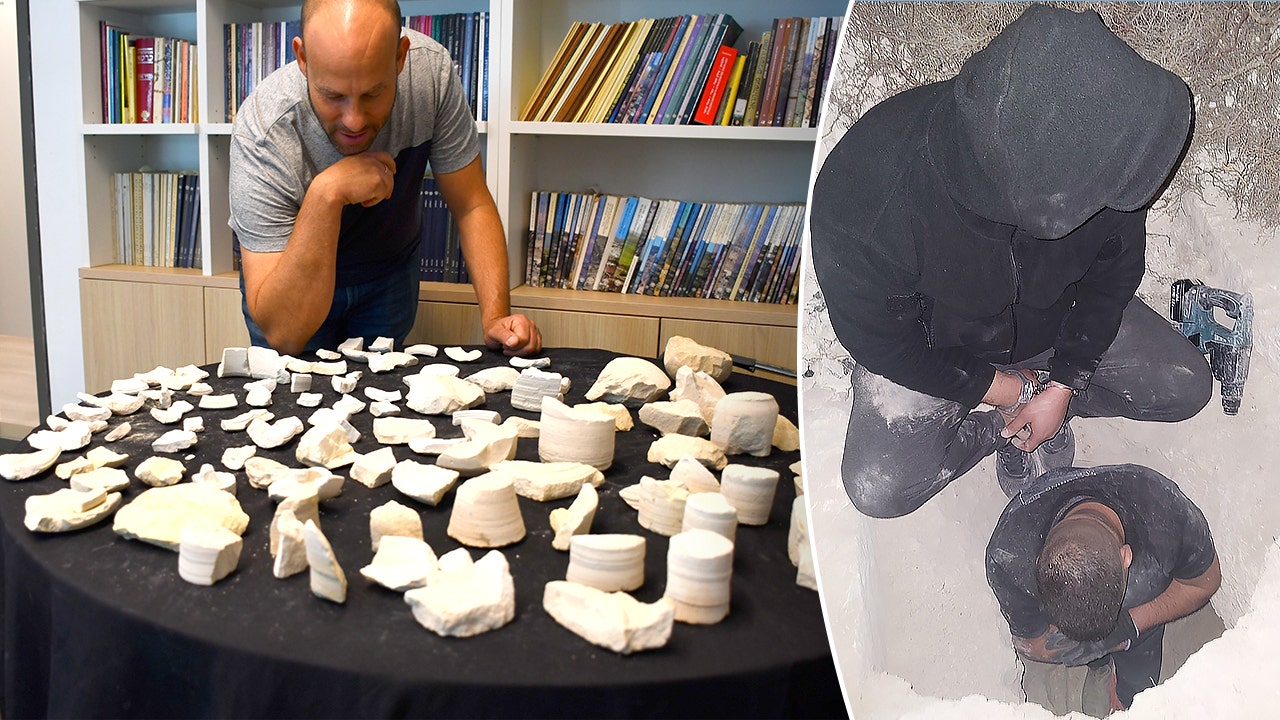
Uncovering a 2,000-year-old stone vessel workshop that once served pilgrims, Israeli authorities caught antiquity thieves red-handed in Jerusalem cave.
Authorities in Israel recently conducted a sting operation against antiquities thieves and uncovered a 2,000-year-old workshop that once supplied pilgrims traveling to Jerusalem.
The Israel Antiquit… [+3850 chars]
Cybersecurity researchers have disclosed details of a new Android trojan called Massiv that's designed to facilitate device takeover (DTO) attacks for financial theft.
The malware, according to ThreatFabric, masquerades as seemingly harmless IPTV apps to dece…
Cybersecurity researchers have disclosed details of a new Android trojan called Massiv that's designed to facilitate device takeover (DTO) attacks for financial theft.
The malware, according to Thre… [+4696 chars]
Cybersecurity researchers have disclosed details of a new mobile spyware platform dubbed ZeroDayRAT that's being advertised on Telegram as a way to grab sensitive data and facilitate real-time surveillance on Android and iOS devices.
"The developer runs dedic…
Cybersecurity researchers have disclosed details of a new mobile spyware platform dubbed ZeroDayRAT that's being advertised on Telegram as a way to grab sensitive data and facilitate real-time survei… [+10631 chars]